Acer’s latest Chromebook Plus goes bigger with a 14-inch display
The Acer Chromebook Plus 514 packs in a bigger display, new Intel processor for AI smarts, and even more storage for $400

Best cassette players 2024: tape players for a retro audio fix
The best tape players will have you rockin’ and a rollin’ in no time (pencils not included)

This new Omega Speedmaster Chronoscope is the perfect way to mark 100 days to Paris 2024 Olympics
As excitement builds for the next Olympic games, Omega has launched a new edition of the Speedmaster Chronoscope

This mechanical keyboard might be Knob by name, but is stylish by nature
It’s a keyboard that’s been designed to look good, but it also sports extras like customisable knobs and a mini screen

Latest posts
Best outdoor TV 2024: weatherproof screens for your backyard or patio
The ultimate screens for outdoor summer entertainment – these are the best outdoor TVs

DJI’s new backup battery can juice up just about any device
It’s a backup battery that can charge your drone, phone, and other small appliances. DJI can juice up just about any gadget you’ve got!

How to get multiple Amazon Echo smart speakers working together
You don’t need a degree to have a smart home – here’s how to get multiple Echo devices working together

The best free iPhone and iPad games 2024 to play today
Got an iPad or iPhone? Load it with the best iOS games – none of which cost a penny!

I think these are the most comfortable running shoes I’ve ever used – and they’re sustainable, too
The $200/£160 unisex Condor 3 is Veja’s third version of the sustainable brand’s neutral running shoe first introduced in 2019

Features
Best gaming console 2024: which console should you choose?
The best gaming consoles to buy, from Xbox and PlayStation, to the Nintendo Switch and more – we’ve played them all. Press start to continue…

PS5 Pro: everything we’ve heard about Sony’s upgraded console
Is a mid-life hardware refresh for the PlayStation 5 on the cards?

Best running headphones 2024: wireless buds for sport and workouts reviewed
Add a soundtrack to your sprints with the best headphones for running

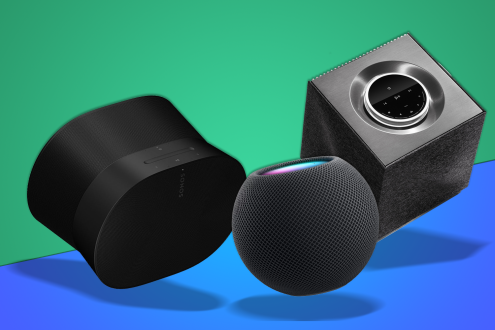
Best wireless speakers 2024: music and radio via Wi-Fi
Streaming speakers for all budgets – our guide to the best wireless speakers you can find anywhere
Reviews
Nothing Ear (a) review: hello yellow
Introduction It was inevitable, really. Once Nothing introduced a second, more affordable model to its smartphone range, a matching pair of wireless earbuds couldn’t be far behind. Ear (a) takes most of what made the firm’s previous audio efforts such great value, ekes out a bit more battery life, and mixes up the styling just […]

Nothing Ear review: definitive article
Third time lucky for Nothing’s ace affordable in-ears

Maserati Grecale Folgore review: tempting transition EV
Luxurious, powerful, and yes, very expensive
Motorola Buds+ review: with a little help from my friends
Moto brings in Bose for affordable ANC expertise

Motorola Edge 50 Ultra hands-on review: ultimate evolution?
Style-led flagship doesn’t go quite has heavy on hardware as some rivals

Motorola Edge 50 Fusion hands-on review: colour me interested
New entry-level Edge promises Pantone approved colours

Motorola Edge 50 Pro review: living on the edge
Mid-range specs meet Pantone-approved cameras

Samsung QN95D review: looks and sounds stunning
Flagship NeoQLED 4K TV adds class-leading processing to get the most out of its bright images and immersive audio

The best of everything
Stuff Picks
Sky Stream and Glass free update slashes delay for live sport by 20 seconds
There are two big free updates coming to Sky Glass and Sky Stream this spring as part of Entertainment OS

Is this the world’s most boring phone?
The Boring Phone goes back to basics and strips out everything smart to help people spend less time on their phone

Sony’s latest super bright Bravia TVs get rid of confusing names
The Mini LED Bravia 9 leads the pack, with the Bravia 8 OLED and Bravia 7 Mini LED sitting underneath

This free Amazon Music update playlist-making AI to rival Spotify
Well, well, well! Amazon Music also offers an AI feature that lets you dictate what music you want it a playlist, and get it picked for you

These gadgets make filming content so much easier for me
If you find yourself regularly filming content, make sure the tech you’re using is actually helping. These gadgets make things much easier











